Crowd-Sourcing Technology

We develop a novel crowdsourcing technology to sense mobile objects as referenced in the following paper:
Mosent technology: J. Tan, W. Wong, X. Zhu, H. Wu, and S.-H. Chan, "Cooperative Target Tracking and Signal Propagation Learning Using Mobile Sensors,'' Proceedings of the ACM on Interactive, Mobile, Wearable and Ubiquitous Technologies (IMWUT), Vol. 2, Issue 3, pp. 136:1-136:21, September 2018.
We employ a novel crowdsourcing system to promote a caring community to find wandering elderly. Below is our system components.
iBeacon Tags
1. Carried by dementia people.
2. Will embed the tags onto daily personal items, such as keychains, wallets, or clothing.
3. The casing of the ibeacons are water resistant and able to work under splashes or short showering.
Mobile app/Android box
1. A standalone app or SDK which contains all 4 modes with different authorization rights.
2. Integration with Google map or local maps.
Server Programs
1. Server localization engine to calculate the location of dementia people.
2. Database structure and implementation.
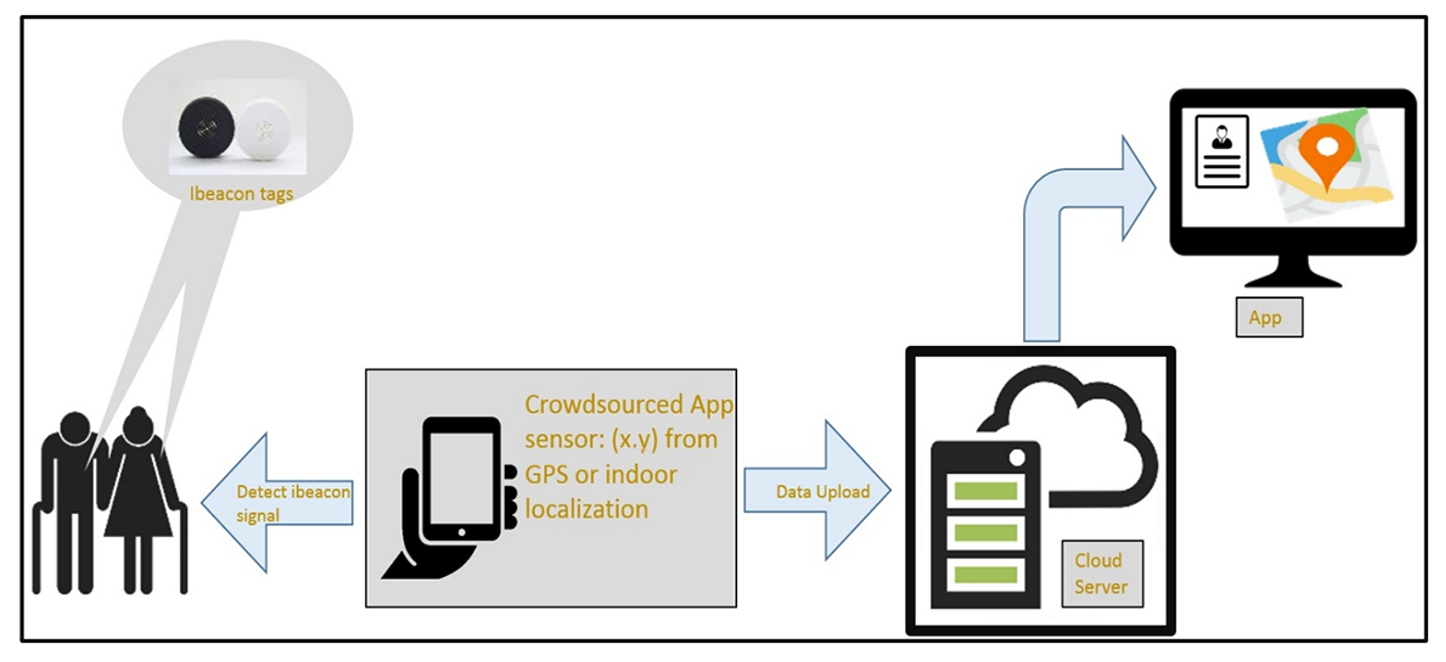
We are developing an IoT-based smart city technology to promote social awareness and community caring for dementia. We work with several parties to enable a crowdsourced environment, including angels, caregivers, agencies and administrator.
Technology Advantages


Complements existing GPS-based solutions by bridging its gaps

Harnessing the power of the crowd: Promoting social awareness, value and cooperation

Long lifetime (tag can last for more than a year without charging)

Highly portable: light weight and small size (around 1 inch diameter)

Low cost (fixed tag cost of around US$20, crowdsourced data from angels with low data rate, and possibly some minimal monthly service charge)

Responsive (beaconing interval 1-3 seconds)

Long range: up to 100m in our experiment (compare to the traditional 30m only)

Cost-effective infrastructure: Phone apps or Android boxes (raspberry pi)

Work both outdoor and indoor

Privacy and security

